It’s great that you are looking into what SOC 2 compliance is (SOC stands for System and Organization Controls).
Perhaps your business is growing, and the enterprise you are closing a deal with requires SOC 2 compliance. Or, maybe you recognize that you’re going to need this to close that big partnership down the road, and so you’re looking into the matter now.
Either way, big thumbs up to you.
To help walk you through these terms, allow us to introduce the one and only Soc the Croc (pictured above in the header). This particular crocodile is a SOC 2 certification officer. They can be pretty rough around the edges, and just might chomp if you don’t do things properly. However, once you get to know Soc better, and take your security obligations seriously, the croc can become your best friend. Your tech and sales teams may even thank you for taming the crocodile.
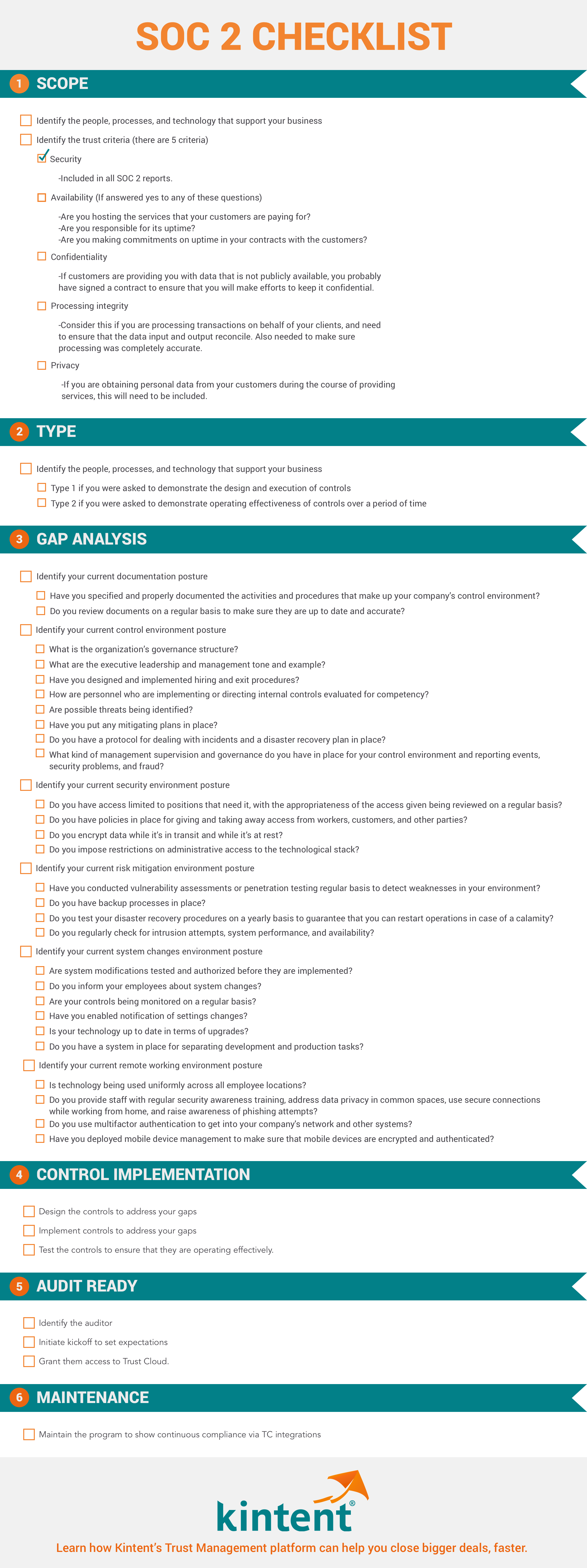
SOC 2 should be viewed as an opportunity, not a problem. Below is a simplified glossary of the terms and acronyms you’ll encounter when you go through preparation for a SOC 2 audit. Becoming familiar with SOC lingo allows you to move forward with more confidence. If you have a SOC 2 checklist, pull it out and follow along. Otherwise, here’s a SOC 2 checklist you can use if necessary.
What is AICPA?
AICPA stands for the American Institute of Certified Public Accountants. SOC audit and reporting standards that define the criteria for managing customer information were designed by this member association.
What is SOC 2?
SOC 2 is a comprehensive framework applicable to all service providers who store any kind of client data in the cloud or on-prem. Moreover, SOC 2 is the most widely adopted and requested compliance certification for SaaS vendors in the United States.
The SOC 2 attestation is an objective, a third-party report created by a CPA accredited auditor vouching that your organization is prioritizing data security, availability, processing integrity, confidentiality, and privacy. This designates that your organization has effective internal controls to protect your customers’ data.
Undergoing the audit and having the report completed by an independent third-party auditor allows you to prove to your stakeholders that you are a reliable service provider and have the necessary controls in place to safeguard their data.
In case you’re interested, here’s a resource to learn about SOC 2 in much greater detail.
SOC 2 Audit Firm
SOC 2 audit firms are regulated by the AICPA, and they are required to be independent CPAs. The SOC 2 auditor you choose to work with will examine your controls (which will include evidence collection) to determine whether they are functioning properly. Documents that the auditor may review include:
- Organizational charts
- Inventory of assets
- Processes for onboarding and offboarding
- Processes for managing change
If you want to learn more about how you can prepare for an audit, or how to choose your auditor, read more on how to apply for a SOC 2 audit.
SOC 2 Report
A SOC report is an audit report done by an objective, third-party firm that would be responsible for assessing your cybersecurity practices. All companies that hold customer information throughout their operation should consider scheduling and go through an audit. Depending on the maturity of the company, the intended audience for the report, and the scope, there are two types of SOC 2 reports to choose from: SOC 2 Type 1 and SOC 2 Type 2.
SOC 2 Type I Report
A SOC 2 Type I report examines the controls that govern an entity’s security and other applicable criteria at a point in time. This involves an auditor performing a walkthrough of your processes to understand and attest to the design of your internal controls. Therefore, it would usually be the first-ever SOC 2 report for a company.
A Type I audit can be the right choice for you if:
- You’re pursuing a SOC 2 audit for the first time, and don’t have the requisite organizational maturity to pass all of the required controls
- You need a report quickly
- You’re going after small-to-medium-sized enterprise deals
- Before preparing for a full audit, you want to show that you understand the necessary procedures to achieve the SOC 2 standard
SOC 2 Type II Report
SOC 2 Type II reports assess the efficacy of an entity’s security and other applicable criteria since the last SOC 2 audit. Most SOC 2 reports are renewed annually. However, it is up to the company to decide to go under audit earlier if there is a necessity.
You will need a Type II attestation if:
- You have mature information security programs, systems, and processes, and can prove that you’re consistently adhering to controls over a long period
- You have other compliance frameworks in the mature state that can contribute to your SOC 2 controls
- You are planning a major funding round or exit
- You’re pursuing enterprise-level deals
In Type I, your controls are verified only once. In contrast, the SOC 2 Type II audit process involves a typical three-to-six month (though it can range up to 12 months) observation period, during which a third-party auditor verifies the effectiveness of your continued adherence to controls throughout the observation period.
SOC Trust Services Criteria (TSC)
There are five Trust Service Criteria (TSC) or Trust Service Principles (TSP) within the SOC 2 framework. All organizations, independent of size, industry, or customer needs pursuing a SOC 2 have to include the Security Criteria. The others are optional and guided by the business and customer requirements.
The five Trust Services Criteria (or Trust Service Principles) are:
Security – Organizations are assessed on their ability to protect against unauthorized access, unauthorized disclosure of information, and damage to systems that could compromise the availability, integrity, confidentiality of customer data.
Availability – Information and systems are available for operation and use to meet the demands of its customers. If your organization is responsible for hosting the data that your customers need as a part of utilizing your services, you may consider including this criterion.
Processing Integrity – Consider this criterion if you are in a transaction-based business. This principle verifies that system processing is complete, valid, accurate, timely, and authorized to meet the objectives.
Confidentiality – Information designated as confidential is protected to meet the entity’s objectives. To achieve organizational success, sensitive information must be appropriately safeguarded from unwanted access.
Privacy – Personal information is collected, used, retained, disclosed, and disposed of to meet the entity’s objectives. If you collect the personal information of customers to provide services, this may be a consideration.
Learn More About SOC 2
While all of the terms shared above are vital to know if you are undergoing a SOC 2 audit, this is just the beginning. The compliance process is nothing to sneeze at — in fact, countless business deals fall through the cracks each year due to a lack of trust and verification of security standards.
While working to achieve the SOC 2 requirements can eat up months of your time and thousands of hours when done manually, TrustCloud was created specifically to ease this pain and shorten the process as much as possible.
With TrustOps, our aim is to get you audit-ready in less than 12 weeks! From automated tests and workflows to generating policies relevant to your business, we’re making it effortless for you to build a program and meet your obligations under SOC 2 quickly.
Next time you want your product and engineering team to help you meet the SOC 2 requirements — there’s no need to lurk in the shadows and attempt to catch them off guard anymore — try out a demo today.