SOC 2 is the most widely-adopted and requested compliance certification for SaaS vendors in the United States. In this post, we will explain the basic concepts involved in the process, outline what you can expect as you work towards compliance, and provide guidance based on our cumulative experience working closely with our customers and auditor partners.
What is SOC 2?
TL;DR. SOC 2 is divided into several Trust Service Criteria. These criteria are then grouped into five categories. Only controls that map to common criteria within the Security category are required for a SOC 2 attestation — a report attesting that all the required controls are in place.
SOC 2 is a comprehensive framework applicable to all service providers who store any kind of client data in the cloud or on-prem. This includes the vast majority of SaaS start-ups. The framework outlines a number of Trust Service Criteria, grouped into five overarching categories with corresponding common criteria, for evaluating and reporting on the robustness of an organization’s systems (read: your technology and business stack) and policies. In a SOC 2 audit, you are only required to show proof of adherence to the Security category.
The five categories are:
- Security: Required. Demonstrates to an auditor that your systems are protected against unauthorized access and other risks that could impact your organization’s ability to provide services to your clients.
- Availability: Optional. Applicable when service organizations need to demonstrate that their systems meet a certain standard of high-availability.
- Confidentiality: Optional. Applicable to organizations that need to demonstrate that data classified as confidential is protected.
- Processing integrity: Optional. Applicable to organizations that must demonstrate that system processing is occurring accurately and in a timely manner.
- Privacy: Optional. Included when a service organization is in possession of personal information, to demonstrate this information is protected and handled appropriately.
At the end of the day, each individual business must choose which category, along with their corresponding set of common criteria, they would like an auditor to evaluate. There isn’t a one-size-fits-all approach, and you will need to decide what aspects of your business you would like observed and audited as part of this process, based on the commitments you have communicated to your customers and other stakeholders.
For example, if you have committed to delivering a secure product that is available 99% of the time, you might consider including common criteria from the Availability principle in your SOC 2 attestation. If your commitments include keeping your customers’ confidential data secure, you might think of adding Confidentiality criteria as well. Finally, if your service creates, collects, transmits, uses, or stores personal information, you should consider adding criteria from the Privacy principle. In every case, the criteria included in the Security principle, which lightly touch on all of the other principles as well, form the required baseline for SOC 2.
Now that you’re familiar with the framework behind SOC 2, it’s time to decide which type of SOC 2 audit you will need to pursue.
Do I choose a Type I or Type II audit?
TL;DR. If you’re a very young company, get a Type I. If you’re pursuing enterprise sales, consider getting a Type II.
This is the question we get asked most frequently here at TrustCloud. So much so that we’ve created a nifty little graphic highlighting the differences.
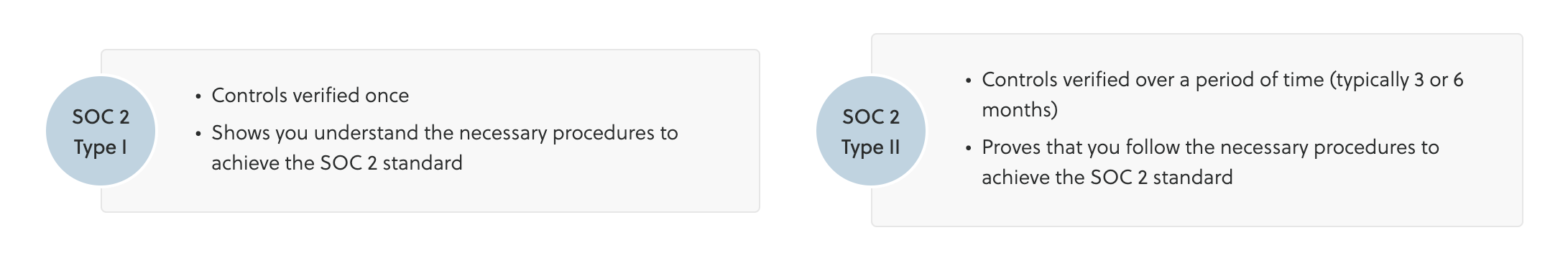
It’s important to understand that there are valid reasons to choose either type of audit, and that you don’t have to have both; many organizations pick one or the other. While Type II is the more popular of the two — it’s more comprehensive, and cheaper in the long run — a Type I audit can be the right choice for you if:
- You’re pursuing a SOC 2 audit for the first time, and don’t have the requisite organizational maturity to pass all of the required controls.
- You need a report quickly.
- You’re going after small-to-medium sized enterprise deals.
- Before preparing for a full audit, you want to show that you understand the necessary procedures to achieve the SOC 2 standard.
In Type I, your controls are verified only once. In contrast, the SOC 2 Type II audit process involves a typical three-to-six month (though it can range up to 12 months) observation period, during which a third-party auditor verifies your continual adherence to controls.
You will need a Type II attestation if:
- You have mature information security programs, systems and processes, and can prove that you’re consistently adhering to controls over a long period of time.
- You are planning a major funding round or exit.
- You’re pursuing enterprise-level deals.
How SOC 2 Unblocks Sales
If you’re selling to the enterprise (large corporations… not the starship), the policies and procedures you craft for your SOC 2 audit can be leveraged to answer the detailed security questionnaires typically required by your customers. These customers want to see that you know the security lingo, have the right systems and tools in place, and know how to document and adhere to processes.
What will this cost me?
Traditionally, SOC 2 can cost anywhere from $30,000 to $100,000 when you factor in the cost of the audit firm, as well as internal costs including productivity, staff training, and resources needed to meet specific requirements.
At TrustCloud, we believe compliance shouldn’t cost an arm and a leg. We want to make the readiness and audit process both affordable and simple. We’ve broken the cost down into two areas:
- A compliance automation platform. By automating much of the process, platforms such as TrustOps help you reduce and better manage your internal costs. We’ve developed a transparent and straightforward pricing structure to make it easier for you to manage the overall cost of the program (read: $12,000/year for SOC 2 with no hidden consulting fees.)
- An auditor. We’ve developed strong relationships with a number of audit firms. Not only does this mean that they are trained on the platform and know how to evaluate your business, they are also able to pass along sizeable discounts as a result of a referral from TrustCloud. SOC 2 audit partners in the TrustCloud network charge between $12,000 – $28,000 for SOC 2 audits, based on the maturity and complexity of the engagement.
If you think about it, we’ve created a win-win-win scenario. Take that, Michael Scott!
How long is the SOC 2 process going to take?
When using tools such as TrustOps, that automate much of the process for you, the timeline for your Type I or Type II certification could look like the following:
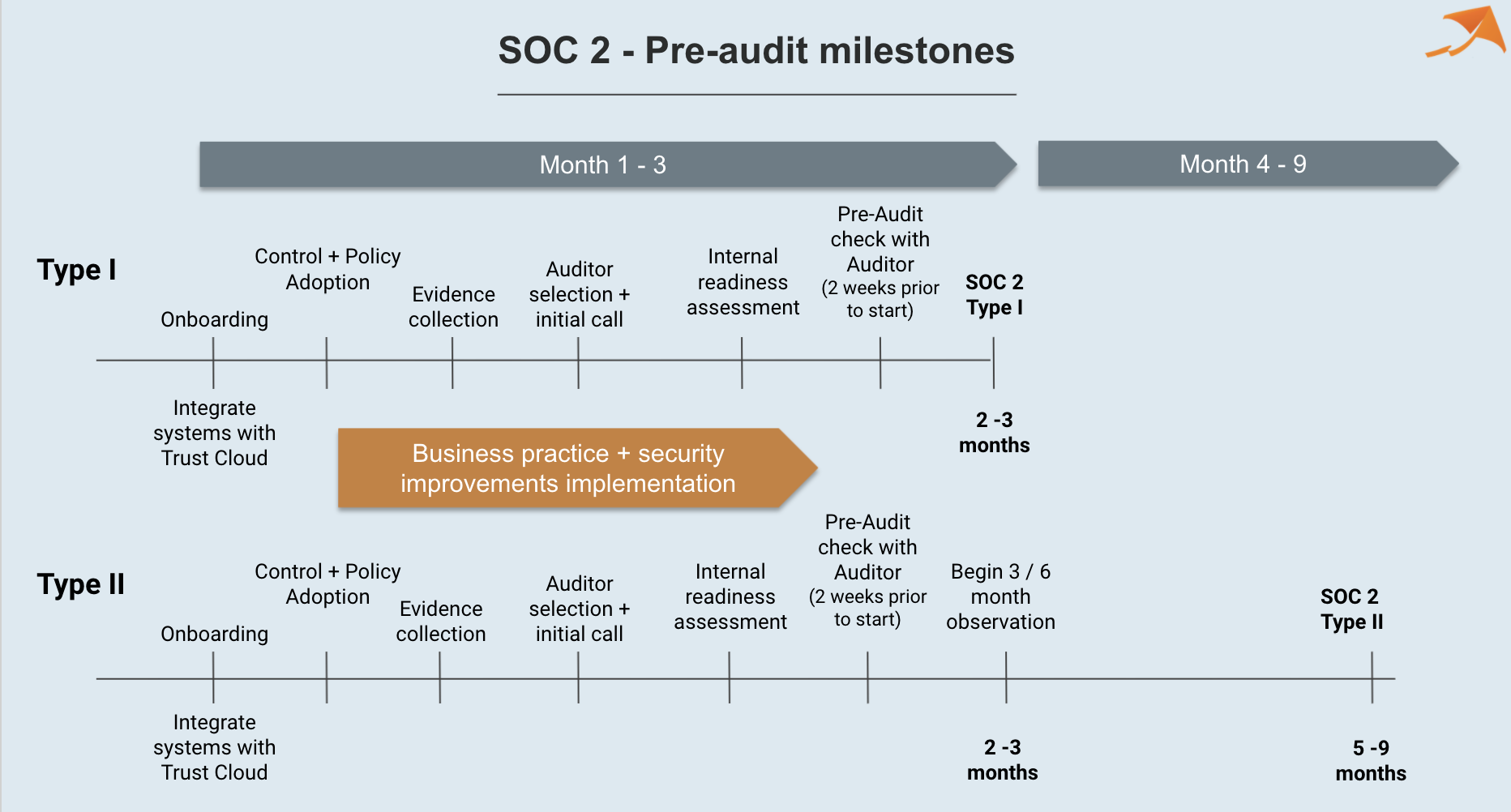
Without TrustOps, you would be looking at a very manual and tedious process that could take up to a year. During this time, you would need to understand each requirement and how it applies to your business, conduct the necessary testing, accumulate all the evidence proving your compliance in a single location, and draft the right documentation. This estimate doesn’t include the time an auditor needs to evaluate your business and observe your practices.
In a very biased nutshell: you should use TrustOps.
How do I prepare for an audit?
TL;DR. Appoint a leader and create a dedicated team. The team will be responsible for creating controls and mapping those to the 43 Common Criteria. Fill in the gaps. Conduct tests. Gather evidence. Document everything.
If you’ve been through a SOC 2 audit before, you are well aware of how tedious and time-consuming it can be for your team and yourself. If you haven’t, think spreadsheets. Spreadsheets everywhere!
The People
After you’ve made the decision to pursue a SOC 2 attestation, here’s something to keep in mind when drafting your audit preparation strategy. You may want to create a taskforce of employees from the IT or security team, with support from team members familiar enough with your technical systems. Having an executive or manager own this process with the team will also be hugely beneficial.
The SOC 2 process requires commitment, and team members may need to take time away from their other tasks to focus on preparing for an audit. You should account for a loss in productivity, and ensure you are staffed accordingly.
The Process
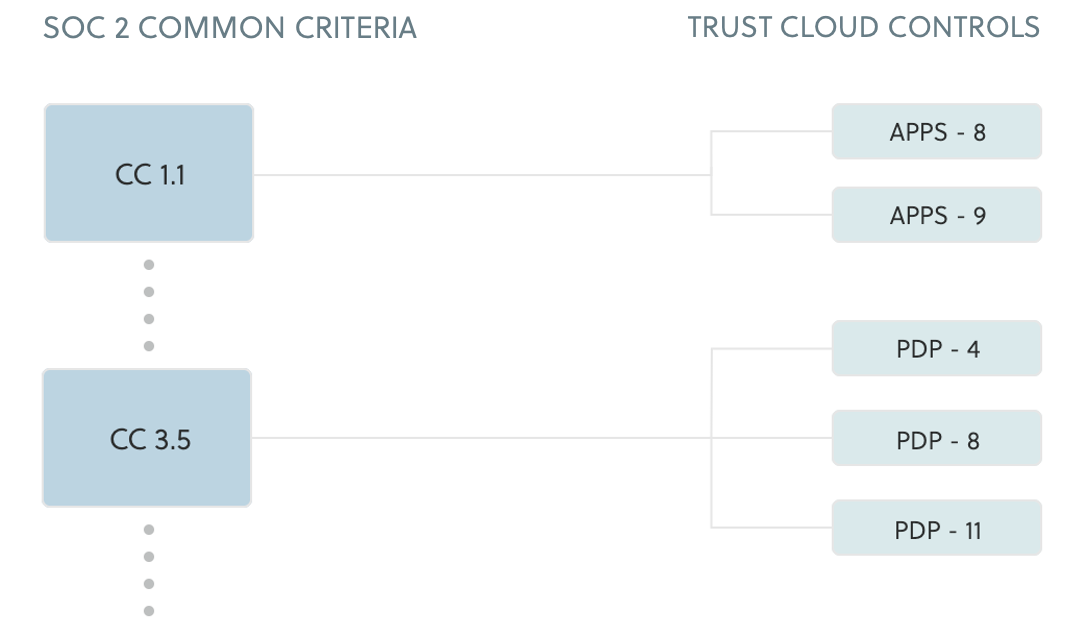
The first thing you will want to do is analyze the 43 Common Criteria, and determine which points of focus are relevant for your business. If this feels like an overwhelming decision, it’s time to phone a friend and ask for help (*cough* Kintent).
Once you know what to focus on, it’s time for control creation, mapping, validation, and adoption. At this stage, you will create and adopt controls that are relevant to your business, determine which systems and business processes need to conform to them, and validate the mapping between your controls and criteria requirements.
What are controls?
Controls are a way to express elements of risk that can impact your business, and account for how these risks can be mitigated. Generally speaking, you may need to implement up to 100 controls as part of your SOC 2 program.
The next step is to fill in the gaps: purchase and implement security tools and services to improve your security and business processes. Some examples of these include performing pen testing, enrolling in asset management, and conducting background checks. At the same time, you should be gathering evidence to show that you are accurately compliant with all relevant controls, writing policies, and documenting procedures that explain how certain controls are satisfied.
What are policies?
A policy is a document that describes how you are mitigating the risk expressed by one or more related controls. As a general guideline, you may need to develop or have 15 – 20 policies in place.
Once complete, it is up to you to conduct the necessary tests and ensure that you consistently pass them. If you’re working with a vendor like TrustCloud (shameless plug), we’ll help you automate much of this work. In TrustOps, we’ve developed a readiness-assessment feature to help you determine if you’re on the right path for an audit (another shameless plug).
When you’re ready, it’s time to select an auditor.
How do I choose my auditor?
Going through an audit can be a nerve-racking process. When it comes to SOC 2, the one thing you have to remember is that at its core, an audit is an auditor’s informed opinion on how well your organization’s controls meet the relevant Trust Service Criteria. There are a few things you should consider when selecting an auditor:
- Accreditation: Ensure that your auditor is a licensed CPA. Only a CPA can sign off on a SOC 2 audit.
- Find a reputable firm. It doesn’t have to be a brand-name firm like KPMG; one with a good reputation will suffice. If you need guidance in this area, we’re happy to provide some recommendations.
- Experience matters. An auditor with more experience is likely to have a better and more thorough understanding of SOC 2, how to evaluate controls against your organization, and the best practices that apply.
- Fit. Auditors are like snowflakes; no two are alike. It’s important that your auditor understands your business, so they can expertly assess if there are any gaps or deficiencies.
What do auditors look for?
TL;DR. Auditors are looking for evidence that proves you’re adhering to the policies and procedures you have selected.
Auditors are guided by the IIA standard Code of Ethics, which tasks auditors with being independent and objective. The documentation you developed as evidence is seen by an auditor as proof that a particular control exists, and helps them evaluate operational effectiveness (whether or not the control is performing as it should).
Using a combination of techniques, an auditor obtains an in-depth understanding of your program and how it fits into the SOC 2 framework. These techniques may include:
- Observation: Observing you perform a task relevant to specific control.
- Inquiry: Interviewing you or your team to learn about a specific process.
- Inspection: Requesting evidence of compliance with a control.
In order to satisfy the auditor’s needs, it’s imperative that documentation is both complete and accurate. The source of the information in the document has to be identified and verified, the content of the document must be written with integrity, and the documentation has to be easily accessible and retrievable for audit purposes. At the end of the day, you want your auditor to come to the same conclusion about the state and health of your information security program as you would. It’s your job to help them come to that conclusion.
At the end of this long journey, once an auditor has reviewed your work and determined that your controls, policies, and procedures meet all requirements, they will give you their stamp of approval. You can now shout from the rooftops (or post on your website) that you are SOC 2 compliant… for now. And then you can start planning for next year’s audit.
Let us help.



