You may have heard about the Health Insurance Portability and Accountability Act, commonly known as HIPAA, and the industry-wide, standardized requirements it imposes on the confidential handling and protection of health information. If you’re not familiar with the subject matter, may we suggest you read our Introduction to HIPAA: The Only Guide You’ll EVER Need.
In this post, we’re going to spend some time outlining the steps you should take when preparing for a HIPAA assessment, and providing guidance around whether you even need an assessment in the first place.
Under HIPAA, companies in the healthcare space (which traditionally include healthcare providers, health plans and healthcare clearinghouses, but also includes digital health startups) need to adhere to regulations on how to manage, store, and transmit protected health information (PHI). We should also mention that HIPAA is enforced by the United States Department of Health and Human Services’ (HHS) Office for Civil Rights (OCR).
The OCR is responsible for issuing annual guidelines to help companies identify and implement ‘the most effective and appropriate administrative, physical, and technical safeguards to secure electronically protected health information (ePHI).’ Under the Health Information Technology for Economic and Clinical Health Act (HITECH), the HHS is required to periodically audit Covered Entities and Business Associates.
That’s right, it’s the ‘always be ready’ rule. Like you didn’t already have enough problems…
What is the HITECH Act?
HITECH is a federal law that amends HIPAA (as part of the final omnibus rule) and is geared towards promoting the adoption of technology by healthcare providers, while also advocating for the improvement of privacy and security for IT systems and PHI.
But what does always being ready mean for you?
We’re so glad you asked!
One of the ways you can ensure that you would successfully pass an audit by the OCR is to assess your systems, policies, and procedures in the same way the OCR would if they were auditing you. You can either do this yourself (commonly known as a self-assessment) or hire an external auditor to do it for you (commonly known as a third-party assessment). HIPAA doesn’t specifically require you to do annual assessments, nor does the OCR recognize “certificates” provided by private organizations, so beware of anyone saying otherwise.
If you choose to do an assessment, here is some helpful advice to get you started.
Step 1: Understanding Requirements
Depending on the type of organization you are, you may have different obligations under HIPAA. Before you start, you need to understand which of the rules apply to you, and scope the level of effort required by your team to meet those rules.
For example, to prove adherence to the privacy rule, you would need to show that you’ve implemented the proper controls, policies, and procedures to protect PHI from wrongful disclosure. Meanwhile, for the security rule, you would need to prove that you’ve implemented the appropriate administrative, physical, and technical safeguards.
Step 2: Information Asset Inventory
Once you’ve identified the HIPAA rule(s) that apply to you, it’s time to perform an inventory of all your information assets to see which relevant systems are housing PHI and ePHI, and understand the risks that apply to them.
To make this a little more straightforward, here are two questions to keep in mind:
- Are there any external sources creating or coming into contact with PHI/ePHI?
For example, do any of your vendors or consultants create, receive, maintain, or transmit PHI/ePHI? - What are the human, natural, and environmental threats to information systems that contain PHI/ePHI?
The Security Rule requires companies to evaluate the risks and vulnerabilities in their environment. Companies and other entities must implement ‘reasonable and appropriate’ security measures to protect against any reasonably anticipated threats to the security of PHI and ePHI.
Once you’ve completed your inventory, the next step is to perform a risk assessment using your newly-compiled inventory (these are the systems housing PHI and ePHI.)
What is a risk assessment?
A risk assessment is an analysis of your entire business, against a particular standard or certification, to identify any gaps or weaknesses and provide you with an idea of where your risks and liabilities lie. We recommend conducting a risk assessment early on, as it will help you establish a baseline and prioritize remediating critical security gaps. Now would also be a good time to start thinking about controls you may want to adopt.
What are controls?
Controls are a way to express elements of risk that can impact your business, and account for how these risks can be mitigated. You may need to adopt up to 75 controls for your HIPAA program.
Even if you don’t do an annual assessment, you should conduct a thorough risk assessment at least once a year to ensure that your systems are secure. If you use a compliance automation platform (and you should), you’ll be able to assess risk more frequently and effortlessly.
Step 3: Additional HIPAA Requirement
Aside from assessing risks that exist in your company, HIPAA requires that you implement a number of processes. We’ve compiled a few of the more commonly requested requirements below:
Training Employees
As a first step, you should identify all employees that will come in contact with PHI. It would also be prudent to include those who would potentially come in contact with PHI as part of their job. Any employee who has exposure to PHI or ePHI should be trained in how to secure both. Their training should cover all the HIPAA safeguards — physical, technical, and administrative.
This training process must be documented, and must be repeated annually. If you’re going with a self-assessment, you should keep this documentation on hand, so you can provide it when requested by an auditor. For third-party assessments, this documentation lets your assessor know that you and your team are up-to-date on all the latest changes in the regulation, and are using information security best-practices.
Our recommendation is to work with an experienced vendor to administer the training. If you’re looking for guidance in this area, we’re happy to connect you with our partners. There may or may not be a discount involved. We were trying to be cheeky there. There one hundred percent is a discount.
Assigning roles and responsibilities to a privacy or security officer.
As you may have noticed, adhering to HIPAA guidelines is a lot of work with a lot of moving parts. The best way to keep the flow of information under control is to assign a dedicated privacy or security officer, who can help keep track of all the moving parts and make sure the company is adequately communicating with vendors and employees regarding their obligations under HIPAA.
When you assign a privacy or security officer, they will:
- Monitor compliance with HIPAA security policies and procedures on an ongoing basis.
- Maintain, implement, and remain up-to-date on all policies, procedures, and documentation related to HIPAA security compliance. Think of it as being an airport traffic coordinator, keeping everything on-time and on schedule.
- Ensure their fellow employees receive HIPAA training on policies and procedures.
Having a privacy or security officer can help manage your company’s HIPAA compliance. It’s a lot of information.
Documenting and reviewing policies and implementation
So your employees are trained. You’ve conducted inventory. What’s next?
It’s time to look at how you safely and securely protect digital or analog information by having documented, easily-accessible policies and procedures.
As a company, securely protecting PHI in all its forms is your responsibility, so it’s a good idea to review all your policies at least annually.
What are policies?
Policies are the set of overarching rules that describe what you, as a company, are doing to mitigate the risk expressed by one or more related controls. As a general guideline, you may need to have up to 20 policies in place.
Some key policies include, but are not limited to:
- Risk management policy
- Incident response policy
- Business continuity policy
- Access control policy
- Asset management policy
Ensuring that all external vendors have signed a Business Associate Agreement (BAA)
A HIPAA BAA is a contract between a Covered Entity and a vendor (Business Associate or Subcontractor) used by that Covered Entity, or by a Business Associate and its Subcontractors.
As a Business Associate, you will be asked to sign BAAs with the Covered Entities you work with or are looking to work with. Additionally, you may be working with external vendors (also known as Subcontractors) yourself, to help you provide services to Covered Entities, and HIPAA applies to them too.
What is a Subcontractor?
A Subcontractor is an entity to whom a Business Associate delegates a function, activity, or service, other than in the capacity of a member of the workforce of the Business Associate. For example, a Business Associate could hire a media shredding company to securely dispose of printed medical records, or a software developer to work on a part of the platform that handles PHI. Subcontractors can be accountants, attorneys, transcription services, email encryption providers, file sharing vendors, backup storage services, and more.
Under HIPAA, you will need to ensure that you sign BAAs with all subcontractors who come in contact with PHI.
Step 4: Conduct a HIPAA Gap Assessment
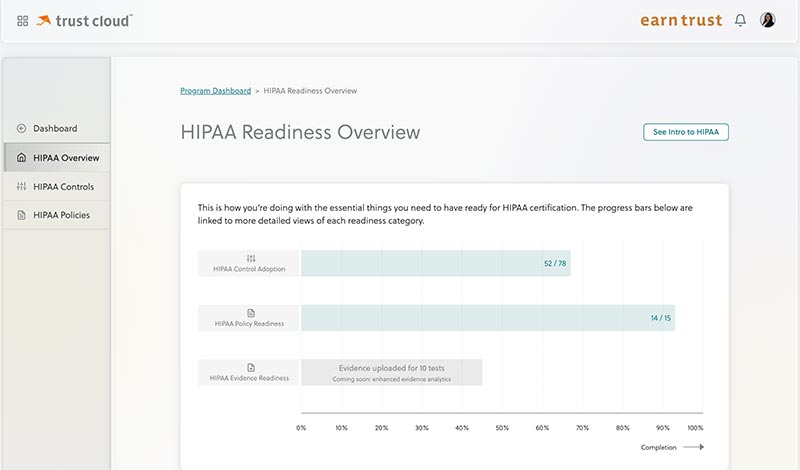
Working in a compliance automation tool gives you the flexibility to conduct periodic gap assessments to help track your overall progress towards HIPAA compliance. The idea is to perform regular comparisons in order to gauge how fast or slow your progress has been, and plan your resources accordingly.
You might be thinking: gap assessments sound complicated; where do I even start? Well — typically, you start by paying a consultant a large sum of money. As an alternative, may we suggest an easy-to-use, joyful compliance automation tool like TrustOps? Exactly like it, in fact. TrustOps helps you adopt, implement, and test controls, and effortlessly maps them to HIPAA requirements.
Here’s what a gap assessment looks like in TrustOps:
Step 5: Evidence collection
Finally, it’s time to show your work! Or rather, get your work to a state where it’s ready to be reviewed. The assessor wants to see proof that you’ve implemented all relevant security requirements, training exercises, policies, and procedures.
A good rule of thumb: if you’ve done something, make sure you have the documentation to prove that it was done. If you trained your employees, keep records listing the type of training, the date the training took place, any certifications earned, and even consider booking an appointment with the employees who went through the training, so they can speak directly with the auditor. You want to be as thorough and detailed as possible.
If you’re using a compliance automation tool (and by now you really should be), it will automatically collect evidence, log activities (such as tests), and compile documents (such as policies and procedures). If running around like a headless chicken is more your style, however, then by all means – open your favorite spreadsheet software and start writing.
Once you’ve finalized all your evidence, you’re ready for your assessment! Your documents are all in order, everyone is trained, and you’re feeling confident. The next step is to decide: do you go with a self-assessment, or choose an independent third-party assessor?
But that, our friends, is a topic for another blog post. May we suggest How to choose your independent assessor or What does an assessor look like?
Fin.